- Banking
- Wealth
- NRI Banking
- Customer Services
We care about your security online
Building a culture of Safety
How DBS secures you: We take all the measures to secure you against any fraudulent activities. It is in our DNA and it starts from our systems, processes and people. We follow best practices across departments and keep our systems, processes and people regularly updated with the latest in security, so that you can bank more and worry less.
How you can secure yourself: While we do everything to safeguard money that you trust with us, we would also want you to be cautious about how you deal with money while you are online, so that you keep yourself away from any online fraudulent activities.
We urge you to follow the mentioned tips to keep your money safe and secure.
RBI Notification - Consumer Awareness - Cyber Threats and Frauds
RBI urges the members of public to practice safe digital banking by taking all due precautions, while carrying out any digital (online / mobile) banking / payment transactions. These will help in preventing financial and / or other loss to them.
Click here to know more about Safe Digital Banking Practise.
RBIs BE(A)WARE booklet on prevention and precaution against financial frauds
The Reserve Bank has released a booklet, “BE(A)WARE” on the common modus operandi used by fraudsters and precautions to be taken while carrying out various financial transactions.
The booklet aims to enhance public awareness about various types of financial frauds perpetrated on gullible customers while carrying out digital payments and other financial transactions. The booklet elaborates on safeguards against commonly used fraudulent techniques, such as, SIM swaps, vishing/phishing links, lottery, etc., including fake loan websites and digital apps.
Your online safety is our top priority, and with the right precautions, you can bank with confidence anytime, anywhere. Stay informed, stay alert, and follow best practices to avoid digital fraud. Open an NRI savings account with DBS Treasures and enjoy secure, worry-free banking.
To read the booklet, click here.
Don’t leave your online security to chance. Here are some useful online and email security tips. Read on to find out how you can prevent any kind of security breach of your information, online.
- Create strong passwords and do not share them with anyone. Remember to change them regularly.
- Monitor your account closely and report any suspicious account activity to the bank immediately. Review the notifications (SMS / Email / In-app) sent by the bank. These notifications are sent for your safety.
- Create separate email accounts for interaction with the bank / official activities and personal activities.
- Never send out confidential account information or personal information on email network without encryption.
- Subscribe to security services like security questions, SMS alerts, etc. offered by email companies, when out of pattern activities are detected in the email account.
- Update your browser, antivirus and security programs frequently. Routinely install all new software and hardware patches or use the automatic update feature when available. Ensure all your software, including its operating system and application software, are updated.
- Be suspicious of unsolicited phone calls, visits, or email messages asking for sensitive information, offering deals that are "too good to be true", or compensating you for assisting someone with moving funds.
- Never reveal personal or financial information in email, and never respond to email solicitations or hyperlinks for this information.
- Visit websites by manually typing the URL into the browser’s address bar instead of clicking on a link in an email.
- Never send sensitive information over the Internet before checking a website's security (Verify "https:").
- Pay attention to the URL of a website. Malicious websites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com vs. .net).
- Verify any suspicious email or information request by contacting the company directly.
- Do not use contact information provided on a website connected to a request; instead, check previous statements for contact information.
- Check for known "Phishing" sites with groups such as the Anti-Phishing Working Group (http://www.antiphishing.org).
- Immediately report suspected fraudulent activity to us and the proper authorities.
- Whenever possible, do not use an unsecured wireless network for financial transactions.
- Be cautious when accessing bank, brokerage, or other financial institution information at Internet cafes, public libraries, hotel business centers, or other public shared computers. If possible, be sure to clear browsing history, cookies, and temporary internet files as personal information can be retained in these shared systems.
Today fraudsters are gaining remote access to victims' phones by tricking them into installing software applications such as TeamViewer or AnyDesk (which are legal apps, not malware, but are remote device control apps). Their modus operandi is as follows:
- Call the victim by claiming to be a Customer Service Officer from a Bank or a Payments bank KYC executive.
- Verify name / date of birth / mobile number and then convince you to download the AnyDesk or TeamViewer app, by scaring you that your account / card will be blocked.
Things to Remember.
- Once you download the apps and give privacy permissions, the app will generate a code that will enable another person to see your mobile screen.
- The fraudster will insist that you share the 9-digit code, so that they can connect and access your mobile screen, without your knowledge.
- As soon as you disconnect the call, the fraudster will start seeing and recording your mobile screen remotely
Always Keep These In Mind.
- The scam happens when you open any mobile banking app or UPI app.
- The fraudster steals your login credentials, then uses your mobile banking login ID to transfer money (as they have access to your mobile screen, they can see all OTP’s and everything that you are doing on the phone secretly).
Please note that the Bank will never call to ask you to download any other app apart from their Mobile banking app and will also never ask you to share any OTP or passwords. Do not share your login credentials with anyone and maintain the privacy of your account.
Business Opportunity fraud involves an offer to become financially independent, or to generate extra income, by setting up your own business.
You receive either a letter or an email, see an advertisement or get redirected to a website where you are asked if you are interested in making easy money by working from home, or setting up your own online business.
The scheme allows you to choose when you work and enables you to fit your work around your other responsibilities. However, the scheme organizer will make you pay an advance fee to register with the scheme and then, depending on your work, either they will find fault with your work and use it as a reason for not paying you or any products or services you are asked to sell will be worthless and you won’t be able to sell them.
Things to Remember
- Be wary of paying money in advance for any job. Most legitimate employers do not require any payment to start working for them.
- Be careful if the scheme operators give web mail email addresses such as @yahoo or @hotmail. Genuine businesses do not use them.
- Beware of adverts for business opportunities that state you can earn a specific or minimum amount of money, just by simply sitting back and letting a business run itself. It is a good indication of fraudsters at work.
- Don’t be tempted by seemingly easy offers for work and read all details before sharing any personal details.
There are many online job scams that take advantage of job seekers in a variety of ways. Scammers have several purposes, depending on the scam - to collect confidential information to use for identity theft, to get you to cash fraudulent checks or to wire or send money, and to get you to pay for services or supplies.
Scammer make upbeat promises about your chances of employment, and virtually all of them ask you to pay them for their services before you get a job. If you must pay for the promise, it’s likely a scam.
Before you apply for a job online, especially work at home jobs, review typical job scams and scam warning signs to help you determine if a job is a scam. If you're not sure, take the time to research the company to make sure the job is legitimate.
Things to Remember
- You're offered a job without an application, interview, or discussion with the employer and You are promised high pay for not much work.
- Stay away from offers that seek sensitive information like details about credit card or bank account, online banking passwords, etc.
- Beware of companies or individuals, who are seeking fees or charges for security deposit / registration / telephonic interview or document verification even though they claim they would provide the refund at later stage.
- Be wary if you are being handed an offer letter without a formal interview and if you have any doubts about the offer or appointment letter, call up the company on its registered landline number.
- Look for spelling mistakes, poor grammar, Company address and contact details of company in the job offer.
- Be cautious about jobs that seem too good to be true and do not open any link provided in the mail.
A digital or virtual currency designed to work as a medium of exchange, cryptocurrency uses cryptography to secure and verify transactions as well as to control the creation of new units.
Essentially, cryptocurrencies are limited entries in a database that no one can change unless specific conditions are fulfilled.
Things to Remember
- Do research and be cautious before investing in cryptocurrencies to make sure your cryptocurrency website is well secured and trustworthy.
- Think before you click! Do not fall for phishing scams or ads laced with malicious links.
- Keep your anti-virus, anti-malware software and firewall current and update it regularly.
- Report phishing scams, and don’t share or forward the lure to others.
- Closely monitor your bank accounts.
- Be wary of social engineering attempts to steal your credentials.
- Routinely scan your computers, laptops, mobile phones, and other devices using updated and patched antivirus / anti-malware software.
Using a Debit Card is a great convenience and a little bit of vigilance on your part can go a long way in preventing fraud and hampering your Debit Card experience.
Things to Remember
- Report loss of the card or if stuck in ATM immediately to the bank. Delays may lead to increased fraud exposure.
- Never write down your PIN anywhere and do not keep your PIN along with your card.
- DBS Bank or our partners will never ask for your Debit Card number, expiry date, card verification value (CVV), one-time password (OTP) or PIN. Never share this information with anyone who claims to be from DBS Bank, RBI, the Income Tax department or any other regulatory bodies, either on phone or email.
- Do not seek assistance from strangers at ATMs - if in doubt contact the bank.
- Never voice out your PIN to merchants or anyone else, even if they claim to be calling from the bank.
- When you are at the ATM, please ensure that no one else is close to you in order to shoulder surf your PIN.
- In case PIN shield is not available, ensure that you cover the keypad during entering the PIN at merchant location / ATM.
- If you do not receive cash from the ATM immediately, please wait for a few minutes and then ensure that the transaction is cancelled.
- If you observe any suspicious activity at the ATM like additional devices fitted and cameras focusing on keypad, do not conduct the transaction, please leave the premises and report to the bank immediately.
- Avoid using ATMs which are in isolated places, dimly lit locations or on the streets without any security guards.
Do not use any ATM which appears to be tampered with, broken, scratched, damaged, sticky with glue, has extra wiring or loose parts around the slot or difficulty in inserting the card.
Financial scams targeting seniors have become prevalent because it is believed that they have a significant amount of money in their accounts and are relatively easy to lure. Staying informed of the below pointers is a good way to ensure the security of their earnings.
Things to Remember
- Never share your password, PIN, OTP, CVV, Card Number over the phone, in texts, by email, or in person even if the caller claims to be calling from the bank.
- Do not write down or save internet banking password in notepads or personal devices.
- Avoid accessing Internet banking accounts from cyber cafes or shared PCs.
- Never sign up for anything unless it is from a reputable source.
- Avoid using ATMs which are in isolated places, dimly lit locations or on the streets.
- Do not seek assistance from strangers at ATMs- if in doubt contact the bank.
- In case you do not receive cash from the ATM please wait for a few minutes and then ensure that the transaction is cancelled.
- Use a mobile device for banking, ensure the device is password-protected and secure.
- Do not tick the box of save password while logging into any sites.
- Don’t click on links, open attachments, or provide sensitive information received from unknown person.
- Use only certified app stores when shopping for apps.
- If you shop or do banking online, make sure you keep an eye on the address bar and that the address looks correct. It should start with https:// which means that it uses encryption to protect your data. The address should also reflect the site you expect to visit. • If you are having trouble with their computer, seek professional assistance. You should not engage with people over the internet to repair their computer unless you know the individual. Be aware that imposters will impersonate notable brands and companies.
- Lookout for common frauds and schemes
- An imposter claiming that a grandchild is endangered or injured, asking for money to help.
- A fake Sweepstakes / Lottery / Car Winner call, in which you are told to provide your personal info so their prize can be delivered.
- A fictitious computer hardware employee stating that a virus has infected your PC.
If you receive a telephone call or email from someone who has some specific information about you, such as your name and details about your friends and family, please beware as using this method, a scammer can trick you into believing he or she is a friend or family member and claim to be in need money for an emergency, such as posting bail, paying a hospital bill, or being detained at an airport. The scammer may pressure you to send money immediately.
Things to Remember
- Resist the urge to act immediately, no matter how dramatic the story is.
- Verify the person’s identity by asking questions that a stranger couldn’t possibly answer.
- Be cautious about sending money to friends and family until you have verified their identity and confirmed that the request is legitimate.
- If you feel uncomfortable about a call you didn't initiate, disconnect the same.
- Check the story out with someone else in your family or circle of friends, even if you’ve been told to keep it a secret.
Under Imposter scams, a fraudster or scammer may claim to be someone you would ordinarily trust or listen to, like a top official / employee of a corporate or banking institution. The impostor can disguise their identity and contact either by phone, email, fax or mail and submit an invoice / request a payment / instruct changes for vendor related payments, so that payments reach the fraudster instead of where it is intended.
Check for Red flags, which include the following but aren’t limited to:
- Changes in the beneficiary details - from commercial to an individual beneficiary.
- Beneficiary’s name, mailing address or account number do not match information available.
- Payment amount does not match the invoice or request received earlier.
- High degree of urgency to make the payment, with a request to keep the payment confidential.
- Subtle changes made to the organization’s name in the email address.
- Changes made to an organization’s email domain to a public domain such as Gmail or mail is received from a similar sounding domain name.
Things to Remember
- Do confirm independently whether a business, utility, government agency or vendor is indeed trying to reach you.
- Use the customer service numbers or email addresses listed on invoices, account statements and legitimate corporate / government websites.
- Independently verify with the top officials like CEO / CFO or persons in whose name the payment request has been made.
- Verify / check email domain, spelling mistakes in domain name, any suspicious or information request by contacting the company directly.
- Do report impostor scams to the company or institution being impersonated.
- Don’t give sensitive information unless you are sure of whom you are dealing with.
- Don’t rely on caller ID to determine if a call is legitimate. Scammers use spoofing tools to make it appear they are calling from a genuine business number.
- Be cautious about unsolicited emails and don’t click on links received from unknown sources.
Investment fraud generally refers to a wide range of deceptive practices that scammers use to induce investors to make investing decisions. These practices can include untrue or misleading information or fictitious opportunities.
It involves someone pretending to offer you the opportunity to invest in a variety of schemes or products that are either worthless or don’t even exist. Some of the types of Investment frauds are Pyramid Schemes, Ponzi Schemes, Pump-and-Dump, Advance Fee fraud and Offshore Scams.
Things to Remember
- Investments with high guaranteed returns with little or no risk.
- Once-in-a-lifetime deals. Scam artists use the tactic of “Do not miss this opportunity – get in now!”, to pressure you into making a quick decision.
- Everyone is buying. You should beware of investment pitches stressing how “other savvy investors have invested, so you should too”.
- Pressure to buy quickly. Scam artists often creates a false sense of urgency by claiming limited supply.
- Overly complex investments and strategies.
A loan scam happens when you are asked to apply for a loan, at low or no interest rates and asked to pay an upfront fee for getting the loan.
These loan scammers set up websites or provide articles and reviews that outline the loans they offer and share SMS / WhatsApp messages / e-mails offering loans to prospects and instruct them to transfer money as a deposit before the loan can be disbursed. After the transfer is done, the scammers are no longer contactable.
Things to Remember
- Do not open or click on e-mail messages from unknown sources that contain a loan offer while lacking specific details.
- Beware if you are asked to transfer money / pay taxes / pay fees for getting a loan.
- If the loan offered has an interest rate far lower than that offered by any legitimate lender, it may be a scam.
- Be wary since legitimate lenders do not offer a loan with no credit checks and free payment periods.
- If you are offered a loan and asked to decide quickly, do not act rashly. Personal loan scams stress upon immediate deadlines that the offer is expiring quickly.
Please remember that legitimate lenders don't send e-mails for offering loans without credit checks, at zero interest rates and do not demand payment to release the loan. Kindly reach out to us in case of any queries.
A lottery or Sweepstakes scam refers to a scam where you may receive notification by mail, telephone, email, text message or social media that you have won a lot of money or a fantastic prize in a competition, lottery or sweepstake. Scammers require you to pay a fee to receive the prize to avoid taxes or additional fees or may even threaten to report you to the Income Tax department or police if you do not make the requested payment.
Things to Remember
- Do not open any emails / messages / attachments from unknown sources / companies, which have a subject announcing you as a winner, if you have never participated in their lottery or sweepstakes.
- Never pay money in-order to receive a prize or winnings as legitimate lotteries do not require you to pay a fee to collect winnings.
- Do an internet search using the names or exact wording of the letter / email to check for any references to a scam – many scams can be identified this way.
- Never send money or give credit card, online account details, or copies of important personal documents to anyone you don’t know or trust and never by email.
- Avoid any arrangement with a stranger that asks for up-front payment via money order, wire transfer, international funds transfer, pre-loaded card or electronic currency. It is rare to recover money sent this way.
Loan Repayment fraud is targeted towards people who may have taken loans.
The fraudsters often use a company name that is like an existing loan offering company and sends out letters / emails claiming that the loan recipient
- has missed a repayment deadline; and
- now owe their original debt plus a ‘penalty charge'
In such an instance
- Check your original paperwork and contact the company, you took the loan from to check repayment dates.
- Ask questions - if someone is legitimate, they won’t pressurize you or be elusive.
- Do not initiate any transfer or make payment without checking with the organization from where you have taken the loan in case of any overdue.
To help you navigate your device in a secure manner, we have created a list of points that will help you always keep your valuable information.
Things to Remember
- Update your mobile devices - Make sure all the mobile devices in your house have the latest reputable mobile antivirus application and keep the antivirus up to date.
- Guard your personal information - Configure your phone to automatically lock if not used for a specified period and if possible, set up a strong alphanumeric password to unlock the device. Be alert especially if a screen on your mobile device suddenly pops up and asks for your confidential information even if you did not open your applications or initiate any activity.
- Think before you download - Before you download an application (app) on your device, review the privacy policy and stay alert from any strange requests for administrator rights or excessive permissions seeking app. Only download apps from reputable sources like Apple App Store or Google PlayStore.
- Check the source - Be aware that fraudsters will continue to create fraudulent applications. Don't download applications onto your phone without checking them out first. Verify the legitimacy of an application by checking the app publisher or seller before downloading it to your mobile phone.
- Clear your device - Clear your mobile frequently by deleting text messages from financial institutions, especially before sharing, discarding, or selling your device.
- Protect your money - Don't follow any links or instructions from unknown or suspicious sources. When banking and shopping on your mobile device, check to be sure the sites are secure. Look for web addresses with https: in the address. If you see a green highlighted browser, this is a safe site. However, yellow and red sites should be avoided.
- Don't use root or jailbreak device - This not only voids your warranty, but also It will make your mobile phone susceptible to an infection from a virus, Trojan, or malware.
- When in doubt, don't respond - Fraudulent texting, calling is on the rise. Just like in fraudulent email, requests for personal information or a call for immediate action are almost always a scam.
- Keep an eye on your phone's performance - Be alert to changes in your mobile phone performance. If you download any new applications and your mobile phone starts performing differently (for example-responding slowly to commands or draining its battery faster or frequent call drops), that could be a sign that malicious code is present on your mobile phone.
- Say no to public Wi-Fi hot spots - Be careful about where and how you conduct transactions. Don’t use your device in an unsecured Wi-Fi network or in a public place, such as in a coffee shop because fraudster might be able to access the information you are transmitting or viewing. It's also a good idea to disable Wi-Fi whenever it's not in use.
- Don't send personal information via SMS (text messaging) - Don’t send account numbers or other sensitive information through regular e-mails or text messages because those are not necessarily secure.
- Always log out - When you are finished checking your balance, transferring funds between accounts, or paying a bill, be sure you logged out of your account.
- Be Always Alert - Get in the habit of monitoring your activity. You'll know immediately if anything looks suspicious. If you suspect an unauthorized transaction, notify your bank right away.
Scammers take advantage of people looking for romantic partners, often via dating websites, chat rooms or social network by pretending to be prospective companions. They create fake profiles with fictional name, or falsely take on the identities of real, trusted people such as military personnel, aid workers or professionals working abroad and play on emotional triggers to get you to provide money, gifts or personal details.
Things to Remember
- Always check for spelling and grammatical mistakes, inconsistencies in their stories and other signs including things like their camera is not working if you want to skype with them or avoidance of meeting in person.
- Do an image search of your admirer to determine if they really are who they say they are. Use image search services like Google Image Search https://images.google.com/) or TinEye Reverse Image Search (https://www.tineye.com/) etc.
- Never share your personal pictures or videos especially if you have never met them before as it can be used for blackmail by scammers.
- Never send money or give online account details or copies of important personal documents to anyone you don’t know or trust.
- Avoid any arrangement with stranger that asks for up-front payment via money order, wire transfer, international funds transfer, pre-loaded card or electronic currency for meeting them or to travel overseas to meet them.
We live in a digital world where we are doing all transactions online. There are many fraudsters out there who use Phishing techniques. It is an attempt to obtain sensitive information such as usernames, passwords and account details by posing as a reputable company via email, text message, phone call, fake websites or social media. Once obtained, your personal and financial information can be used to access your account and steal money.
To safeguard your account from such fraudulent attempts, please note:
Things to Remember
- Review your bank details periodically for any transactions that are not initiated by you.
- Look for secure session indicators like https:// and padlock on websites that require personal information.
- Use updated anti-virus software and firewall software.
- Communicate information such as credit card numbers or account information only via a secure website or IVR.
- Ensure that your browser is up to date and security patches applied.
- If you reveal your bank account details mistakenly, report it to the bank immediately.
- Always TYPE the bank's address (www.dbs.com/india) to access and login to your account, rather than clicking through a hyper-link.
- Be on the lookout for typos or grammatical errors, awkward writing and poor visual design.
- Never click on hyperlinks within emails, instead verify the URL independently.
- Never click or forward links in an email, instant message, or chat from unknown senders.
- Never respond to offers of money from abroad.
- Never respond to / make remittances / participate in schemes or offers from unknown entities.
- Do not reply to emails or SMS' claiming that the recipient has won a substantial sum of money in an online lottery or promotion.
- Avoid filling out forms in email messages that ask for personal financial information.
Never reply to emails which claim to provide your personal information due to system upgrade or your account will be closed if fail to provide information.
Phishing is the attempt of fraudsters to steal your personal information such as logins, passwords, and credit card details, to ultimately take your money. Fraudsters can reach out to you by impersonating a trustworthy entity, such as DBS via digital channels like emails, text messages and fake websites that will redirect to a non-DBS website.
Phishing during COVID-19
At DBS, your safety is paramount to us. In these difficult times, it is very important for you to be aware of ways to spot a fraud communication so that you can be safe from these malicious mails. With this thought, we would like to take a moment to caution you on the risks associated with opening fraud emails sent on the subject of Coronavirus.
Check the sender of email carefully before clicking on anything, phishing emails are known to contain malicious attachment/links, which are capable of installing malware/ransomware, that can access and lock files on your system. This is then followed by cyber-criminals demanding a ransom to allow you access to your files.
If you are planning to contribute to the PM-CARES fund, be careful of fake UPI IDs. Since the announcement of the fund, some fraudsters have been reported to have setup fake UPI IDs. The correct UPI ID of the PM-CARES fund is "pmcares@sbi".
Things to Remember
Don’t leave your online security to chance. Here are some useful online and email security tips.
- Create strong passwords and do not share them with anyone. Remember to change your passwords regularly.
- Monitor your account closely and report any suspicious account activity to the bank immediately.
- Review the notifications (SMS / Email / In-app) sent by the bank. These notifications are sent for your safety.
- Double check the site URL before logging in or sending out information.
- Update your browser, antivirus and security programs frequently.
- Create separate email accounts for interaction with the bank / official activities and personal activities.
- Watch out for phishing messages and do not open links / attachments from unsolicited / unknown sources.
- Never send out confidential account information or personal information on email network without encryption.
- Subscribe to security services like security questions, SMS alerts, etc. offered by email companies, when out of pattern activities are detected in the email account.
Secure your online banking transactions from fraudsters by following some important tips:
- Monitor your bank account closely and report any suspicious activity to the bank.
- Create a unique password for all the different systems & websites you use.
- Strengthen your password using a combination of upper and lower cases, numbers and special characters.
- Do not use easy passwords which includes your name, nickname, phone numbers, date of birth, etc.
- Change your passwords at regular intervals.
- Never share your password over the phone, in text, by email or in person.
- Do not write down your passwords in notepads or personal devices.
- Avoid accessing your bank accounts from cyber cafes or shared computers.
- Do not tick boxes to save passwords while logging into any websites.
- Review all notifications sent by the bank, through emails or messages.
Ransom malware, or ransomware, is a type of malware (malicious software) that prevents users from accessing their system or personal files and demands ransom payment in order to regain access.
How does Ransomware affect my system?
There are several different ways that ransomware can infect your computer -
- One of the most common methods is through malicious spam, or malspam, which is unsolicited email that is used to deliver malware sent by unknown senders.
- The email might include booby-trapped attachments, such as PDFs or Word documents and might also contain links to malicious websites.
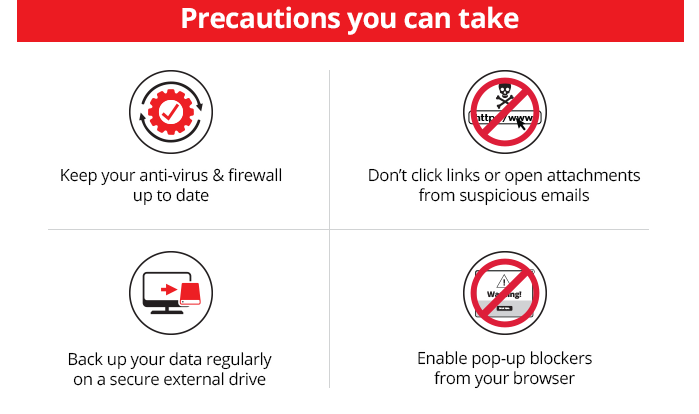
Things to Remember
- Keep your anti-virus software and firewall current and update it regularly.
- Back up your essential data regularly to a secure external drive.
- Enable pop-up blockers to avoid an entry point for ransomware.
- If you receive an email from a person or company you do not know or trust, always exercise caution, avoid clicking on links, sharing personal information and never open the email attachments.
- Be cautious if an attachment asks you to enable macros as it is the most common way that ransomware is spread.
Always Keep These in Mind
- Do not pay the ransom, if you become the victim of a ransomware attack.
- Restore your data, if your data is backed up externally or in cloud storage, if held to ransom.
- Contact your internet security vendor, if you do not have a backup of your data, to see if they have a decryption tool for the ransomware that has attacked you.
Social engineering is the term used for a broad range of malicious activities accomplished through human interactions. It uses psychological manipulation to trick users into making security mistakes or giving away sensitive information.
Some of the ways in which social engineering is carried out are:
- Forged phone calls
- Baiting (false promises), Scareware (false alarms & fictitious threats), Pretexting (gathering personal information on the pretext of lies)
- Phishing / Spear Phishing
- Social Networking sites
- Facebook, Twitter etc.
Things to Remember
- Do not discuss / share sensitive information with others in public or over email / phone calls.
- Ensure nobody is looking when you are typing in your password / Pin - avoid Shoulder Surfing.
- Always check / assure yourself of a caller’s identity, when you receive / answer a call you are not expecting.
Tabnabbing is a computer exploit and phishing attack, which persuades users to submit their login details and passwords to popular websites by impersonating those sites and convincing the user that the site is genuine.
Tabnabbing targets people who keep multiple tabs open in their browser, often for long periods of time. The fraudsters then use JavaScript to change the contents and label of an open, but not active, tab to resemble the log-in screen of a bank, email provider or online shopping store.
Things to Remember
- Ensure anti-virus and anti-spyware software is up to date on your computer.
- If you’re unsure about whether a log-in screen is legitimate (after it being unused for some time), close the tab, open a new one and type in the legitimate URL of the website you want to login to.
- Stay alert and identify unrecognizable transactions from your account.
A technical support scam refers to any class of telephone fraud activities in which a scammer claims to offer a legitimate technical support service, often via cold calls to unsuspecting users, claiming that they have detected viruses or other malware on your computer, or your software is outdated and asks for remote access to your computer to resolve the issue.
Scammer will direct you to open a system log or asks you to use command prompt to generate suspicious looking output to convince you with issues. They will ask you to give remote access of your computer. Once access is provided, the scammer may request you to make payment for technical assistance, install malicious software, change the settings of your compute to make it vulnerable, and / or steal your financial information.
Things to Remember
- Never give control of your computer to a third party unless you initiated the call to fix issues on your computer.
- If you get an unexpected or urgent call from someone who claims to be tech support, hang up. contact the company using legitimate sources such as phone numbers found on the company’s website.
- If you get a pop-up message that tells you to call tech support, ignore it. Do not call a number that pops up on your screen in a warning about a computer problem.
- Never purchase any software or services from an unsolicited call or email or third party.
- Never provide your personal or financial information, including your online banking password, to anyone claiming to be technical support.
What is UPI - Unified Payments Interface (UPI) is an instant payment system developed by the National Payments Corporation of India (NPCI), an RBI regulated entity.
UPI is built over the IMPS infrastructure and allows you to instantly transfer money between any two parties' bank accounts.
Things to Remember
- Always set up your own UPI account, and never take anyone’s help.
- UPI Pin is used for authorization of a payment and funds will always be deducted if you use the UPI Pin.
- Never share or forward any SMS / OTP that you receive on your phone or your CVV or UPI Pin.
- UPI Pin will always be used only on the app’s UPI Pin page.
- Be careful while approving UPI requests for transfer of funds via SMS.
- Never click on the links that you receive via SMS from anyone you do not know.
- Never share any OTP’s generated for UPI payments to merchant websites, over calls.
- For receiving credits, no OTP’s will be generated and sent to your phone.
Beware of Fraudsters - If you receive a call from someone asking for card or bank details, or set up a new VPA, please disconnect and do not engage in any conversation.
Stay aware! Stay Safe!
NRI Banking
Resident Indian Account
Need Help?
Contact us 1860 267 1234 / 1800 209 4555
Only from SG 800 852 6186
For Int'l +91 44 6685 4555
Or have someone contact you
Others
- Other Banking Accounts
- Currency Exchange Rate
- Related Links
- Changes in ODI
- Changes in LRS
- RTGS / NEFT Facilitation centre
- Security and You
- Careers
- Social Good
- Cyber Security
- Sitemap
- Annual Report
- Banking Forms
- Commission Structure for Investments Products
- Commission Structure for Insurance Products
- Grievance Redressal
- Important Announcements
- Unclaimed Deposits - RBI's UDGAM
- Unclaimed Deposits - Search Customer
- Regulatory Disclosure
- Time limit for loan disposal & service delivery
- Treasures Savings Account Charges & Fees
- Current Account
- Interest Rates
- Unparliamentary Language
- List of Repossessed Properties
